Headline
CVE-2020-22253: Hangzhou Xiongmai Technology Co.,LTD.-Security Advisory – Vulnerability of some XM product before year 2017
Xiongmai Technology Co devices AHB7008T-MH-V2, AHB7804R-ELS, AHB7804R-MH-V2, AHB7808R-MS-V2, AHB7808R-MS, AHB7808T-MS-V2, AHB7804R-LMS, and HI3518E_50H10L_S39 were all discovered to have port 9530 open which allows unauthenticated attackers to make arbitrary Telnet connections with the victim device.
Security Advisory – Vulnerability of some XM product before year 2017****2020/ 02/ 20
SA Number: XM-SN-EA60F402001
Initial Release Date : 2020-02-20
Summary
Some deivce have open Telent port 9530, for debugging and diagnosing and technical support for our customers, attacker could use this 9530 port as a vulnerability.
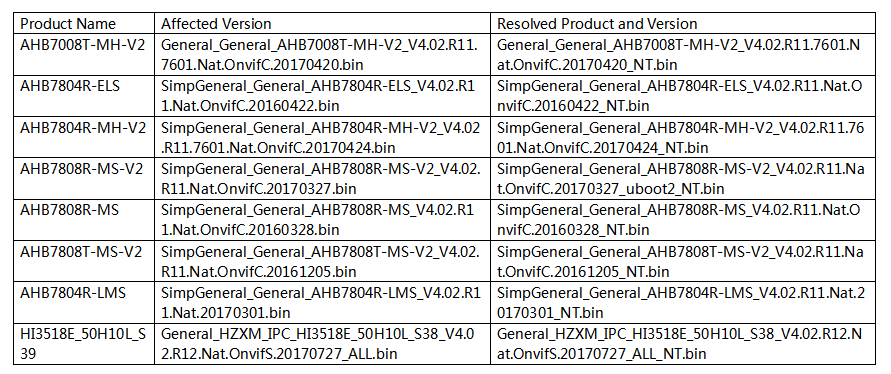
Software Versions and Fixes
Please contact our Technical Support Engineer for those below model for fixes, and update your devices.
Impact
1.High Vulnerability for H.264 devices which firmware released early than May 2017.
2.Low Vulnerability for H.265 devices which firmware released after than May 2017.
3.No risks for devices without open 9530 Telnet Port.
Vulnerability Scoring Detials
The vulnerability classification has been performed by using the CVSSv3 scoring system
(http//www.first.org/cvss/specification-document)
Base Score::9.8(AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H)
Temporal Score: 9.1(E:F/RL:O/RC:C)
Obtaining Fixed Software
Customers please contact our XM Technical Support Engineer to request the upgrades.
Source
This vulnerability was disclosed by Resercher Mr. Vladislav Yarmak
Very appreciated for Mr. Vladislav Yarmak for helping us to disclose this vulnerability, and the positive communication and guide to us, discuss with us for risks of this vulnerability and solutions, even more practical security advices!His suggestions are helping us to strengthen our security levels of our products in present and in future!
Again thanks for the dedication of Mr. Vladislav Yarmak!
We also appreciated the support from Huawei PSIRT to participate as coordinator for the coordinated vulnerability disclosure.
Revision Histroy
2020-2-20 V1.0 INITIAL
The previous:Statement of the third party IPC connect NETIP protocol
The next:Statement
Return list