Tag
#firefox
CSZ CMS version 1.3.0 suffers from a remote command execution vulnerability. Exploit written in Python.
What you look for online is up to you—just make sure no one else is taking a peek.
Ubuntu Security Notice 6509-1 - Multiple security issues were discovered in Firefox. If a user were tricked into opening a specially crafted website, an attacker could potentially exploit these to cause a denial of service, obtain sensitive information across domains, or execute arbitrary code. It was discovered that Firefox did not properly manage memory when images were created on the canvas element. An attacker could potentially exploit this issue to obtain sensitive information.
Plus: North Korean supply chain attacks, a Russian USB worm spreads internationally, and more.
### Summary Google Analytics element Attribute Injection leading to XSS ### Details Since the custom status interface can set an independent Google Analytics ID and the template has not been sanitized, there is an attribute injection vulnerability here, which can lead to XSS attacks. 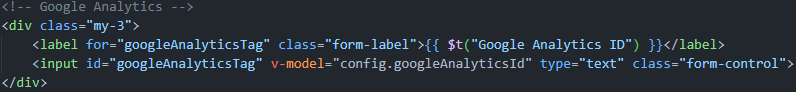 ### PoC 1. Run the latest version of the louislam/uptime-kuma container and initialize the account password. 2. Create a new status page. 3. Edit the status page and change the Google Analytics ID to following payload(it only works for firefox. Any attribute can be injected, but this seems the most intuitive): ``` 123123" onafterscriptexecute=alert(window.name+1),eval(window.name) a="x ``` 4. Click Save and return to the interface. XSS occurs. screenshots:  ![9d0603e634fb7da2e83a0a...
Google has set a date for the introduction of Manifest V3 which will hurt the capabilities of many ad blockers.
Here are the innovations we’ve made in our products recently. Are you making the most of them?
SuiteCRM is a Customer Relationship Management (CRM) software application. Prior to version 8.4.2, Graphql Introspection is enabled without authentication, exposing the scheme defining all object types, arguments, and functions. An attacker can obtain the GraphQL schema and understand the entire attack surface of the API, including sensitive fields such as UserHash. This issue is patched in version 8.4.2. There are no known workarounds.
Memory safety bugs present in Firefox 119, Firefox 115.4, and Thunderbird 115.4. Some of these bugs showed evidence of memory corruption and we presume that with enough effort some of these could have been exploited to run arbitrary code. This vulnerability affects Firefox < 120, Firefox < 115.5, and Thunderbird < 115.5.0.
The black fade animation when exiting fullscreen is roughly the length of the anti-clickjacking delay on permission prompts. It was possible to use this fact to surprise users by luring them to click where the permission grant button would be about to appear. This vulnerability affects Firefox < 120, Firefox < 115.5, and Thunderbird < 115.5.0.