Tag
#js
Red Hat Security Advisory 2024-1490-03 - An update for firefox is now available for Red Hat Enterprise Linux 8.2 Advanced Update Support, Red Hat Enterprise Linux 8.2 Telecommunications Update Service, and Red Hat Enterprise Linux 8.2 Update Services for SAP Solutions. Issues addressed include integer overflow, out of bounds write, and use-after-free vulnerabilities.
Red Hat Security Advisory 2024-1489-03 - An update for firefox is now available for Red Hat Enterprise Linux 8.6 Extended Update Support. Issues addressed include integer overflow, out of bounds write, and use-after-free vulnerabilities.
Red Hat Security Advisory 2024-1488-03 - An update for firefox is now available for Red Hat Enterprise Linux 8.8 Extended Update Support. Issues addressed include integer overflow, out of bounds write, and use-after-free vulnerabilities.
Red Hat Security Advisory 2024-1487-03 - An update for firefox is now available for Red Hat Enterprise Linux 9.0 Extended Update Support. Issues addressed include integer overflow, out of bounds write, and use-after-free vulnerabilities.
### Summary An attacker with admin privileges can upload an attachment containing JS code without extension and the application will render it as HTML which allows for XSS attacks. ### Details When attachments are uploaded without an extension, the application renders it as HTML by default. Therefore allowing attackers to upload .html files containing javascript code to perform XSS attacks. The direct file path to the uploaded attachment is also easily obtainable as it is made up of substrings of the file's MD5 hashes. ### PoC 1. Admin users can upload attachments containing XSS payloads in files without extensions to bypass the .html extension check. 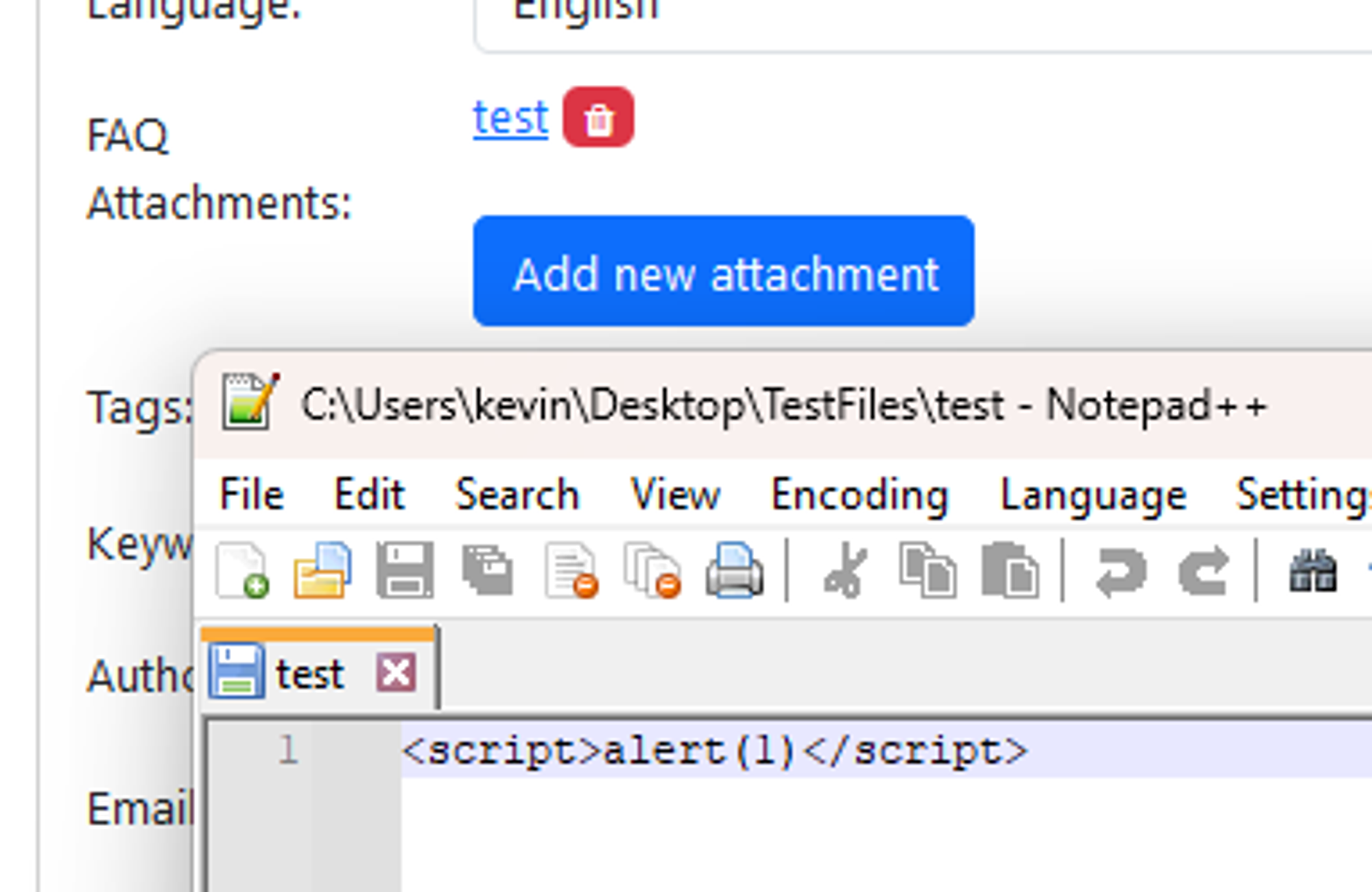 2. Since the path of the uploaded file is built entirely on the file’s MD5 hash and the attachment directory, it is possible for an attacker to know the direct path of the uploaded file. E.g file MD5 hash: 38fff51cb7248a06d6142c6bdf84...
### Impact Navigation history, most viewed and favorite navigation items are returned to storefront user in JSON navigation response if ID of storefront user matches ID of back-office user.
### Impact Versions of Express.js prior to 4.19.2 and pre-release alpha and beta versions before 5.0.0-beta.3 are affected by an open redirect vulnerability using malformed URLs. When a user of Express performs a redirect using a user-provided URL Express performs an encode [using `encodeurl`](https://github.com/pillarjs/encodeurl) on the contents before passing it to the `location` header. This can cause malformed URLs to be evaluated in unexpected ways by common redirect allow list implementations in Express applications, leading to an Open Redirect via bypass of a properly implemented allow list. The main method impacted is `res.location()` but this is also called from within `res.redirect()`. ### Patches https://github.com/expressjs/express/commit/0867302ddbde0e9463d0564fea5861feb708c2dd https://github.com/expressjs/express/commit/0b746953c4bd8e377123527db11f9cd866e39f94 An initial fix went out with `[email protected]`, we then patched a feature regression in `4.19.1` and added ...
### Summary While examining the "App Link assetlinks.json file could not be found" vulnerability detected by MobSF, we, as the Trendyol Application Security team, noticed that a GET request was sent to the "/.well-known/assetlinks.json" endpoint for all hosts written with "android:host". In the AndroidManifest.xml file. Since MobSF does not perform any input validation when extracting the hostnames in "android:host", requests can also be sent to local hostnames. This may cause SSRF vulnerability. ### Details Example <intent-filter structure in AndroidManifest.xml: ``` <intent-filter android:autoVerify="true"> <action android:name="android.intent.action.VIEW" /> <category android:name="android.intent.category.DEFAULT" /> <category android:name="android.intent.category.BROWSABLE" /> <data android:host="192.168.1.102/user/delete/1#" android:scheme="http" /> </intent-filter> ``` We defined it as android:host="192.168.1.102/user/delete/1#". Here, the "#" character at the end of the hos...
Debian Linux Security Advisory 5644-1 - Multiple security issues were discovered in Thunderbird, which could result in denial of service, the execution of arbitrary code or leaks of encrypted email subjects.
Debian Linux Security Advisory 5643-1 - Multiple security issues have been found in the Mozilla Firefox web browser, which could potentially result in the execution of arbitrary code or information disclosure, bypass of content security policies or spoofing.