Tag
#git
Info stealers are thriving on Mac, with one specific variant accounting for 70% of all info stealer detections at the end of 2024.
The education sector is changing quickly as it adopts digital tools for better learning experiences. These days, learning…
Google warns that hackers tied to Russia are tricking Ukrainian soldiers with fake QR codes for Signal group invites that let spies steal their messages. Signal has pushed out new safeguards.
## Summary Nokogiri v1.18.3 upgrades its dependency libxml2 to [v2.13.6](https://gitlab.gnome.org/GNOME/libxml2/-/releases/v2.13.6). libxml2 v2.13.6 addresses: - CVE-2025-24928 - described at https://gitlab.gnome.org/GNOME/libxml2/-/issues/847 - CVE-2024-56171 - described at https://gitlab.gnome.org/GNOME/libxml2/-/issues/828 ## Impact ### CVE-2025-24928 Stack-buffer overflow is possible when reporting DTD validation errors if the input contains a long (~3kb) QName prefix. ### CVE-2024-56171 Use-after-free is possible during validation against untrusted XML Schemas (.xsd) and, potentially, validation of untrusted documents against trusted Schemas if they make use of `xsd:keyref` in combination with recursively defined types that have additional identity constraints.
Attackers are using patched bugs to potentially gain unfettered access to an organization's Windows environment under certain conditions.
At least eight ongoing lawsuits related to the so-called Department of Government Efficiency’s alleged access to sensitive data hinge on the Watergate-inspired Privacy Act of 1974. But it’s not airtight.
A flea market buyer found medical information about hundreds of patients on second hand decommissioned hard drives.
## Summary Problem: Potential man-in-the-middle attacks due to missing SSL certificate verification in the project codebase and used third-party libraries. ## Details In the past, `aiohttp-session`/`request` had the parameter `verify_ssl` to control SSL certificate verification. This was a boolean value. In `aiohttp` 3.0, this parameter was deprecated in favor of the `ssl` parameter. Only when `ssl` is set to `None` or provided with a correct configured SSL context the standard SSL certificate verification will happen. When migrating integrations in Home Assistant and libraries used by Home Assistant, in some cases the `verify_ssl` parameter value was just moved to the new `ssl` parameter. This resulted in these integrations and 3rd party libraries using `request.ssl = True`, which unintentionally turned off SSL certificate verification and opened up a man-in-the-middle attack vector. Example: https://github.com/home-assistant/core/blob/c4411914c2e906105b765c00af5740bd0880e946/hom...
### Description Authentication using Spid and CIE is based on the SAML2 standard which provides for two entities: Identity Provider (IdP): the system that authenticates users and provides identity information ( SAML assertions ) to the Service Provider, essentially, it is responsible for managing user credentials and identity; Service Provider (SP): The system that provides a service to the user and relies on the Identity Provider to authenticate the user, receives SAML assertions from the IdP to grant access to resources. The library `cie-aspnetcorerefers` to the second entity, i.e. the SP, and implements the validation logic of the SAML assertions present within the SAML response . The following is a summary diagram of an authentication flow via SAML: 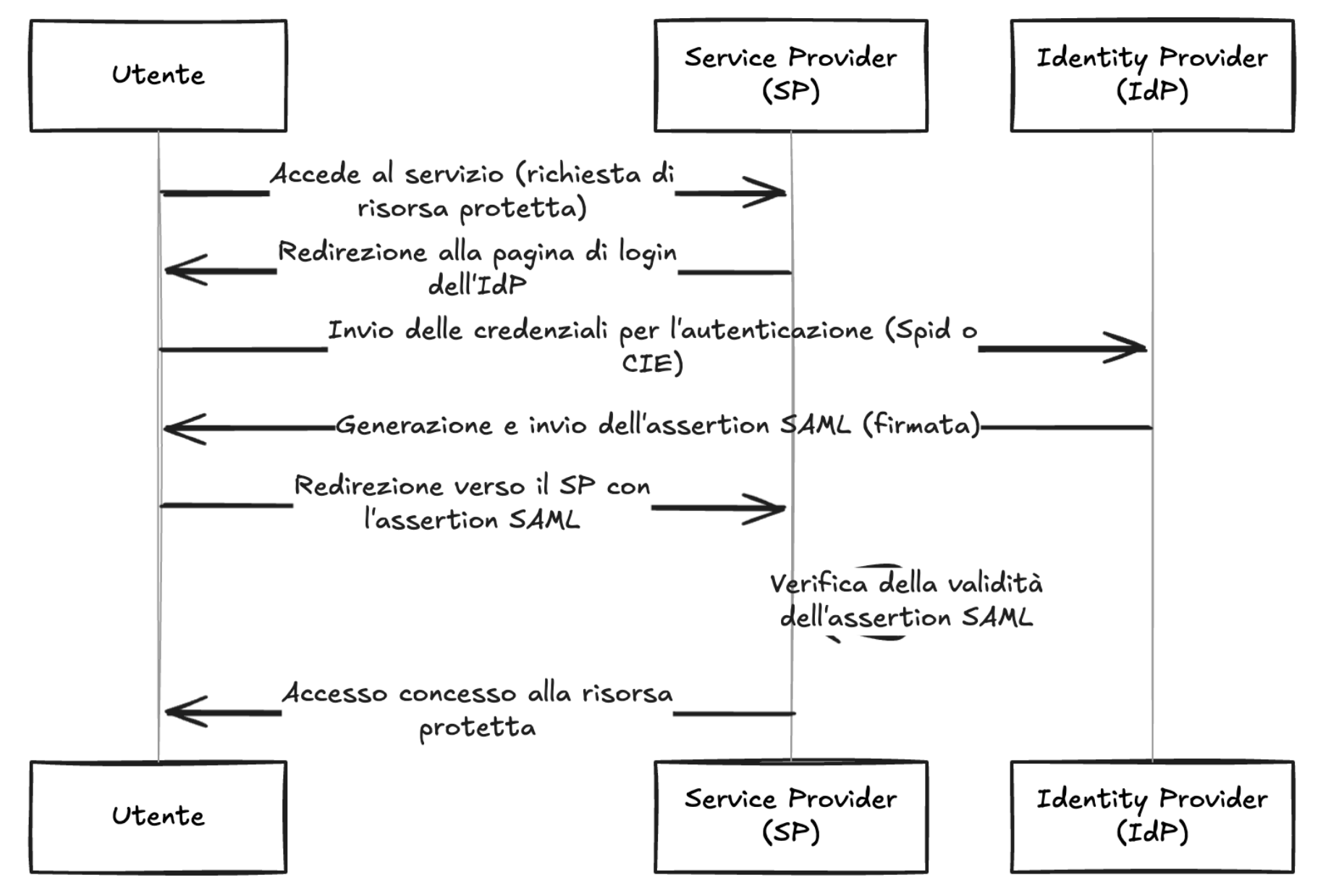 As shown in the diagram, the IdP, after verifying the user's credentials, generates a signed SAML response, this is propagated to the SP by the use...
### Description Authentication using Spid and CIE is based on the SAML2 standard which provides for two entities: Identity Provider (IdP): the system that authenticates users and provides identity information ( SAML assertions ) to the Service Provider, essentially, it is responsible for managing user credentials and identity; Service Provider (SP): The system that provides a service to the user and relies on the Identity Provider to authenticate the user, receives SAML assertions from the IdP to grant access to resources. The library `spid-aspnetcorerefers` to the second entity, i.e. the SP, and implements the validation logic of the SAML assertions present within the SAML response . The following is a summary diagram of an authentication flow via SAML: 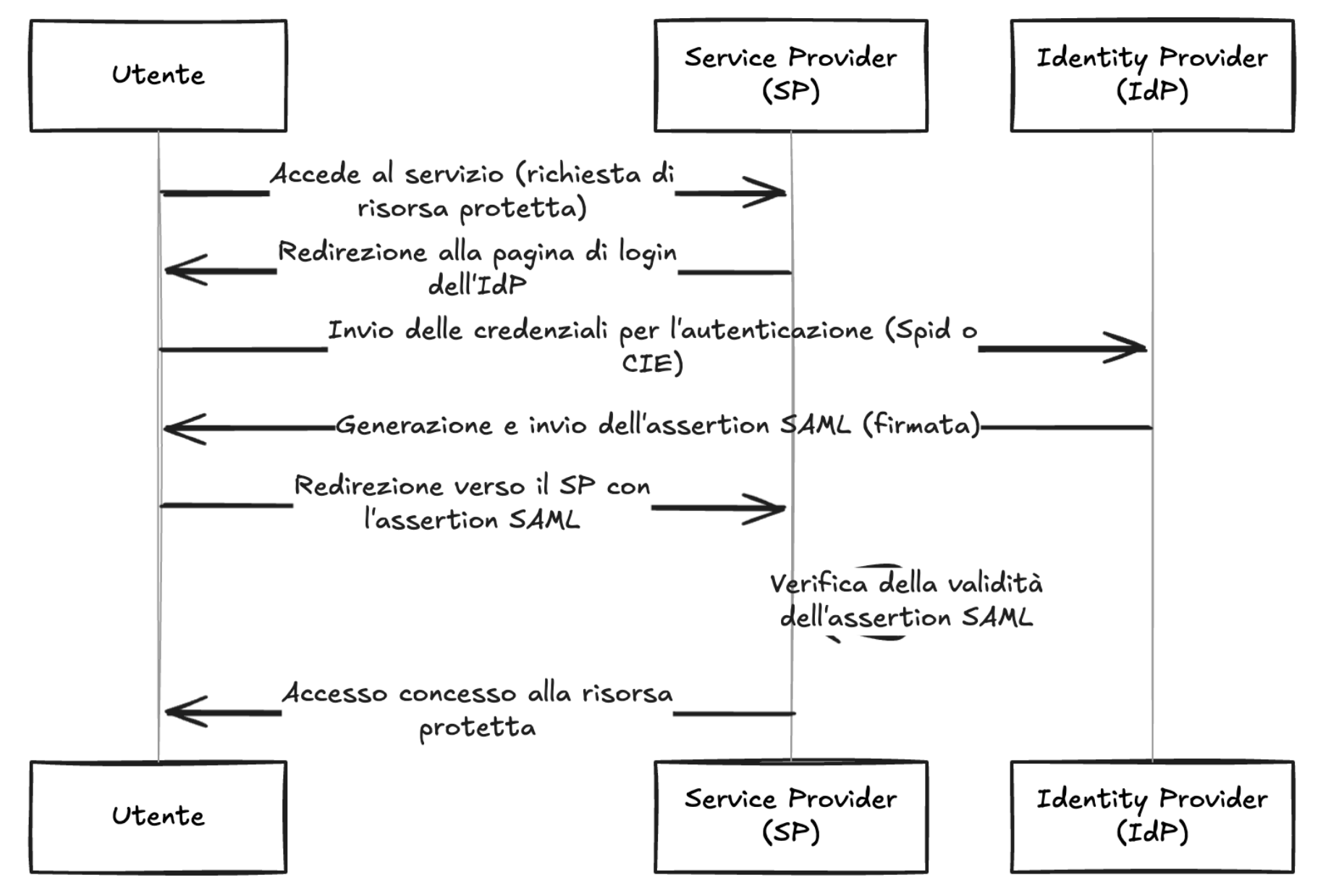 As shown in the diagram, the IdP, after verifying the user's credentials, generates a signed SAML response, this is propagated to the SP by the us...