Headline
CVE-2022-27927: Microfinance Management System in PHP Free Source Code
A SQL injection vulnerability exists in Microfinance Management System 1.0 when MySQL is being used as the application database. An attacker can issue SQL commands to the MySQL database through the vulnerable course_code and/or customer_number parameter.
Submitted by Adam Chengula on Tuesday, March 22, 2022 - 10:48.
****Introduction****
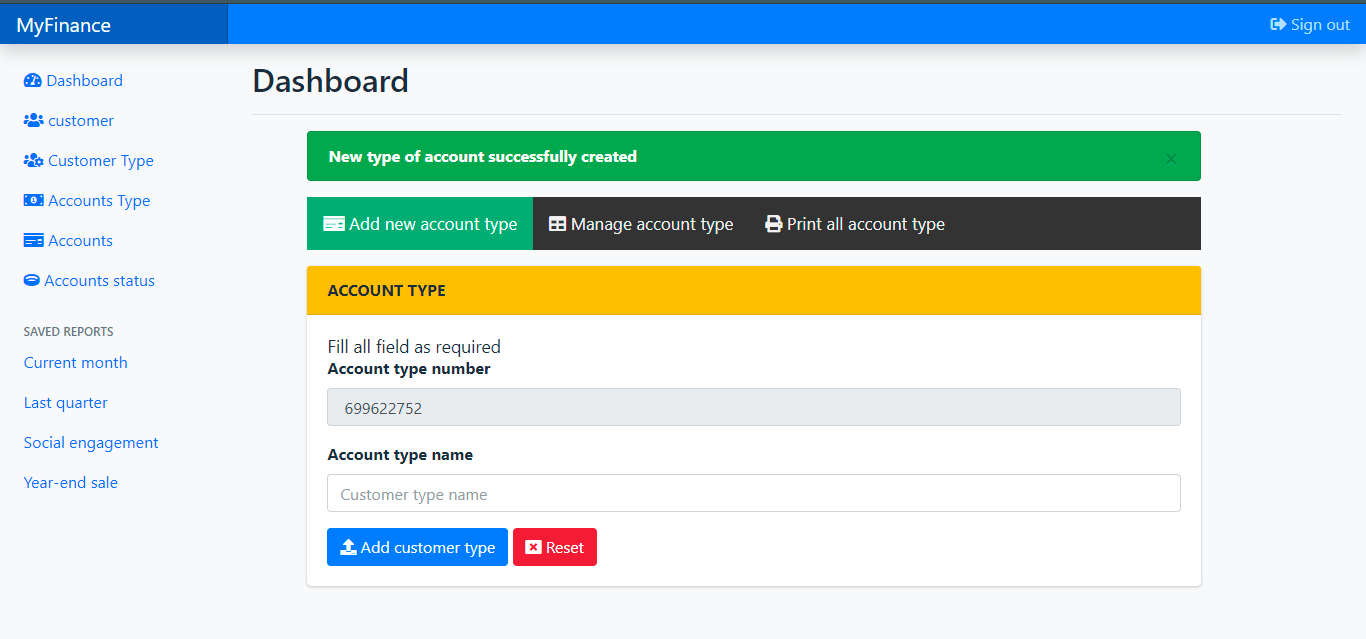
This simple project is a Microfinance Management System. This is a web application that provides an online platform for Microfinance Businesses to manage their clients’ accounts. It allows the management to easily store and retrieve their client records. It has a simple and pleasant user interface using Bootstrap. It also has user-friendly features and functionalities.
****About the Microfinance Management System****
I developed this project using the following:
- XAMPP v3.3.0
- PHP
- MySQL Database
- HTML
- CSS
- Bootstrap
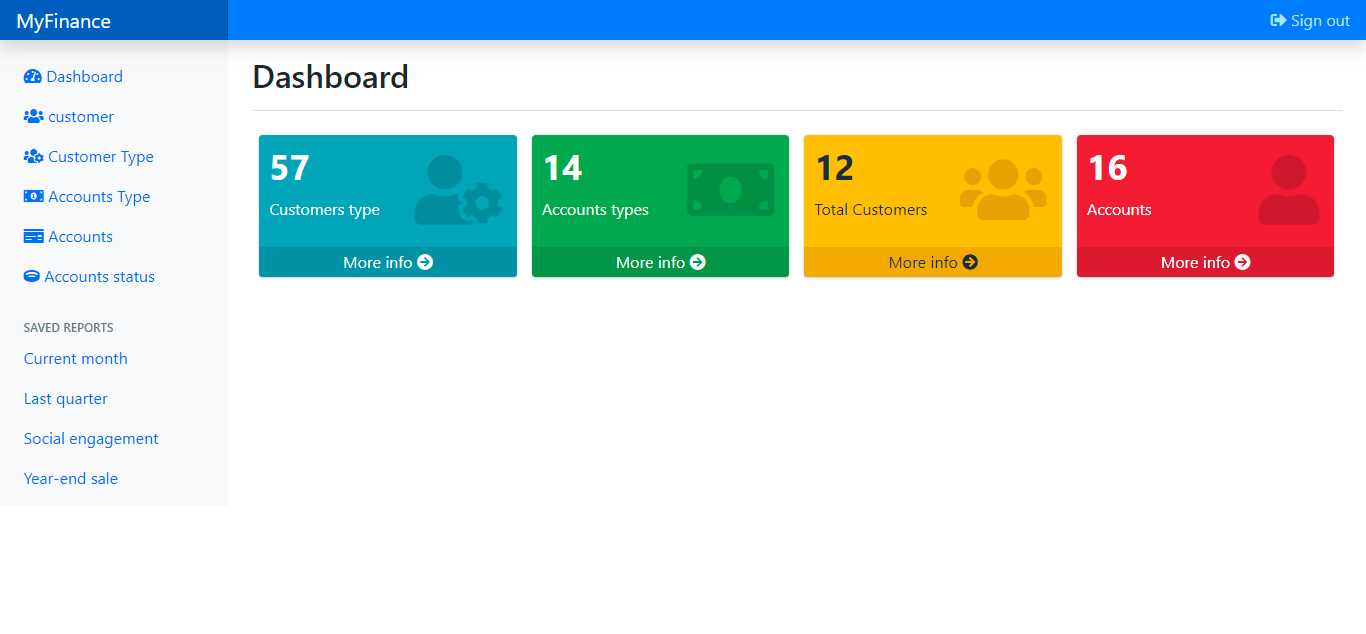
This Simple Microfinance Management System has many different features and functionalities. The application contains CRUD (Create, Read, Update, and Delete) operations for each list. The management can store, retrieve, and manage records of customer/client, account status, and account type lists. Each List in the application has a Generated Printable List using TCpdF Library. The application also contains a simple Dashboard Page that displays the summary of the list.
****Features******Management-Side**
- Secure Login and Logout
- Dashboard
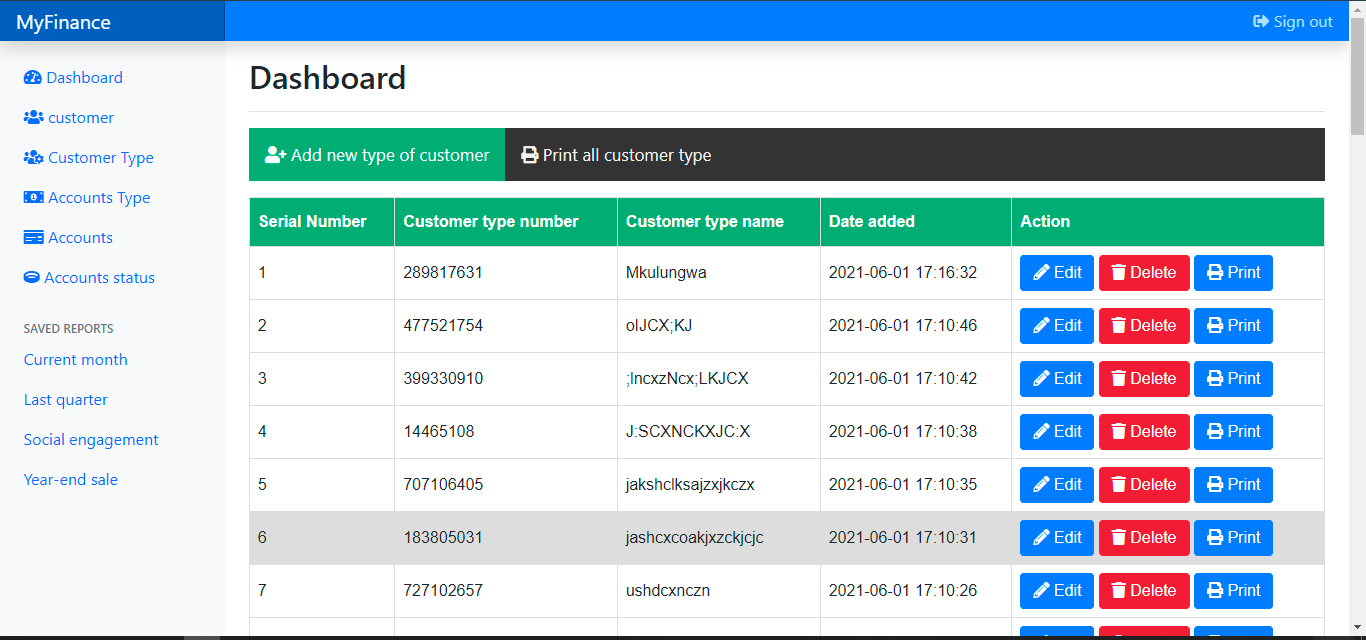
- Customer Type Management
- Add new Customer Type
- List All Customer Types
- Print Customer Type Details
- Update Customer Type Details
- Delete Customer Type Details
- Customer Management
- Add new Customer
- List All Customers
- Print Customer Details
- Update Customer Details
- Delete Customer Details
- Account Type Management
- Add new Account Type
- List All Account Types
- Print Account Type Details
- Update Account Type Details
- Delete Account Type Details
- Account Status Management
- Add new Account Status
- List All Account Statuses
- Print Account Status Details
- Update Account Status Details
- Delete Account Status Details
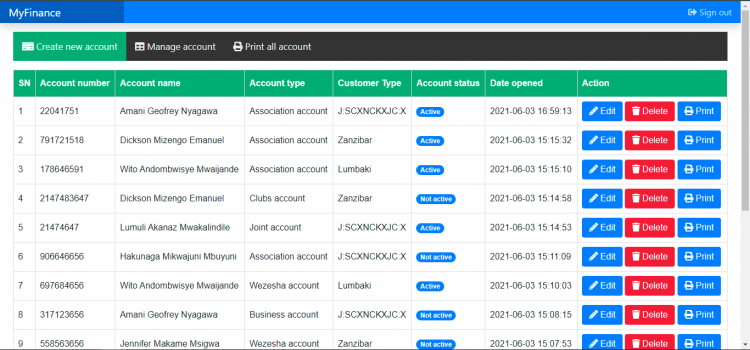
- Account Management
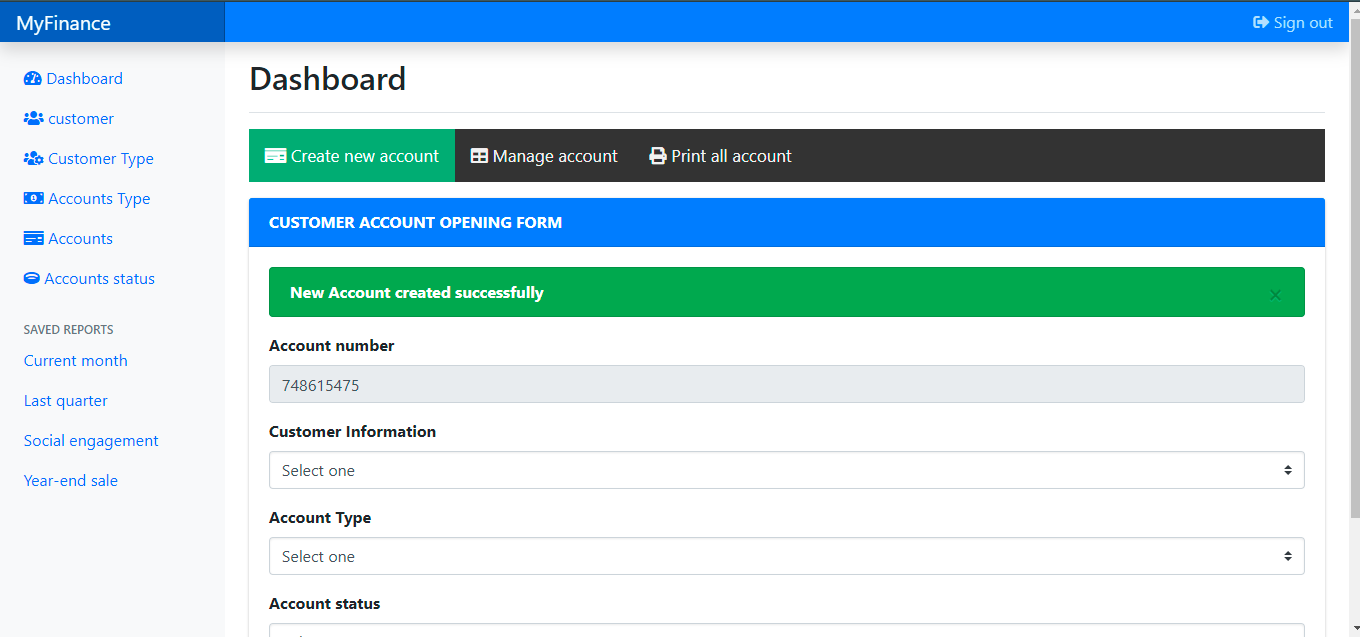
- Add new Account
- List All Accounts
- Print Account Details
- Update Account Details
- Delete Account Details
Note: The Reports Feature is not included in the source code.
The source code was developed only for educational purposes only. You can download the source code for free and modify it the way you wanted.
System Snapshots of some Features
How to Run ??
****Requirements****
- Download and Install any local web server such as XAMPP/WAMP.
- Download the provided source code zip file. (download button is located below)
****Installation/Setup****
- Open your XAMPP/WAMP’s Control Panel and start ****Apache**** and ****MySQL****.
- Extract the downloaded source code zip file.
- If you are using XAMPP, copy the extracted source code folder and paste it into the XAMPP’s “htdocs” directory. And If you are using WAMP, paste it into the “www” directory.
- Browse the ****PHPMyAdmin**** in a browser. i.e. ****http://localhost/phpmyadmin****
- Create a new database naming ****mims****.
- Import the provided ****SQL**** file. The file is known as ****mims.sql**** located inside the database folder.
- Open the extracted Source Code folder and extract the asstes.zip file to the same location. This file contains the libraries that are used in this application.
- Browse the Microfinance Management System in a browser. i.e. ****http://localhost/mims/****.
****Default Admin Access****
Username: admin
Password: 123456
****DEMO VIDEO****
That’s it. You can now explore the features and functionalities of this Microfinance Management System in PHP. I hope this will help you with what you are looking for and you’ll find something useful for your future projects.
Explore more on this website for more Free Source Codes and Tutorials.
Enjoy :)
- 2516 views
Related news
An update is now available for Red Hat Enterprise Linux 8.4 Extended Update Support. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section.This content is licensed under the Creative Commons Attribution 4.0 International License (https://creativecommons.org/licenses/by/4.0/). If you distribute this content, or a modified version of it, you must provide attribution to Red Hat Inc. and provide a link to the original. Related CVEs: * CVE-2021-4083: kernel: fget: check that the fd still exists after getting a ref to it * CVE-2022-0492: kernel: cgroups v1 release_agent feature may allow privilege escalation * CVE-2022-25636: kernel: heap out of bounds write in nf_dup_netdev.c
An update for kernel is now available for Red Hat Enterprise Linux 6 Extended Lifecycle Support. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section.This content is licensed under the Creative Commons Attribution 4.0 International License (https://creativecommons.org/licenses/by/4.0/). If you distribute this content, or a modified version of it, you must provide attribution to Red Hat Inc. and provide a link to the original. Related CVEs: * CVE-2020-0466: kernel: use after free in eventpoll.c may lead to escalation of privilege * CVE-2021-0920: kernel: Use After Free in unix_gc() which could result in a local privilege escalation * CVE-2021-4155: kernel: xfs: raw block device data leak in XFS_IOC_ALLOCSP IOCTL * CVE-2022-0492: kernel: cgroups v1 release_agent feature may ...
An update for the container-tools:2.0 module is now available for Red Hat Enterprise Linux 8.4 Extended Update Support. Red Hat Product Security has rated this update as having a security impact of Moderate. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section.This content is licensed under the Creative Commons Attribution 4.0 International License (https://creativecommons.org/licenses/by/4.0/). If you distribute this content, or a modified version of it, you must provide attribution to Red Hat Inc. and provide a link to the original. Related CVEs: * CVE-2022-27649: podman: Default inheritable capabilities for linux container should be empty * CVE-2022-27651: buildah: Default inheritable capabilities for linux container should be empty
An update for the 389-ds:1.4 module is now available for Red Hat Enterprise Linux 8.4 Extended Update Support. Red Hat Product Security has rated this update as having a security impact of Low. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section.This content is licensed under the Creative Commons Attribution 4.0 International License (https://creativecommons.org/licenses/by/4.0/). If you distribute this content, or a modified version of it, you must provide attribution to Red Hat Inc. and provide a link to the original. Related CVEs: * CVE-2021-4091: 389-ds-base: double free of the virtual attribute context in persistent search
Invicti Acunetix before 14 allows CSV injection via the Description field on the Add Targets page, if the Export CSV feature is used.
An update for kernel-rt is now available for Red Hat Enterprise Linux 8.4 Extended Update Support. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section.This content is licensed under the Creative Commons Attribution 4.0 International License (https://creativecommons.org/licenses/by/4.0/). If you distribute this content, or a modified version of it, you must provide attribution to Red Hat Inc. and provide a link to the original. Related CVEs: * CVE-2021-4083: kernel: fget: check that the fd still exists after getting a ref to it * CVE-2022-0492: kernel: cgroups v1 release_agent feature may allow privilege escalation * CVE-2022-25636: kernel: heap out of bounds write in nf_dup_netdev.c
Red Hat OpenShift Virtualization release 2.6.10 is now available with updates to packages and images that fix several bugs and add enhancements. Red Hat Product Security has rated this update as having a security impact of Moderate. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section.This content is licensed under the Creative Commons Attribution 4.0 International License (https://creativecommons.org/licenses/by/4.0/). If you distribute this content, or a modified version of it, you must provide attribution to Red Hat Inc. and provide a link to the original. Related CVEs: * CVE-2021-33195: golang: net: lookup functions may return invalid host names * CVE-2021-33197: golang: net/http/httputil: ReverseProxy forwards connection headers if first one is empty * CVE-2021-33198: golang: math/big.Rat: may cause a panic or an unrecoverable fatal error if passed inputs...
An Access Control vulnerability exists in Desire2Learn/D2L Learning Management System (LMS) 20.21.7 via the quizzing feature, which allows a remote malicious user to disable the Disable right click control.
An update is now available for Red Hat Ceph Storage 3. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section.This content is licensed under the Creative Commons Attribution 4.0 International License (https://creativecommons.org/licenses/by/4.0/). If you distribute this content, or a modified version of it, you must provide attribution to Red Hat Inc. and provide a link to the original. Related CVEs: * CVE-2021-20288: ceph: Unauthorized global_id reuse in cephx
The Migration Toolkit for Containers (MTC) 1.5.4 is now available. Red Hat Product Security has rated this update as having a security impact of Moderate. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section.This content is licensed under the Creative Commons Attribution 4.0 International License (https://creativecommons.org/licenses/by/4.0/). If you distribute this content, or a modified version of it, you must provide attribution to Red Hat Inc. and provide a link to the original. Related CVEs: * CVE-2021-36221: golang: net/http/httputil: panic due to racy read of persistConn after handler panic
Swimlane’s Asia-Pacific presence grows 173%, highlighting rising demand for low-code security automation.
Certain WSO2 products allow unrestricted file upload with resultant remote code execution. This affects WSO2 API Manager 2.2.0 and above through 4.0.0; WSO2 Identity Server 5.2.0 and above through 5.11.0; WSO2 Identity Server Analytics 5.4.0, 5.4.1, 5.5.0, and 5.6.0; WSO2 Identity Server as Key Manager 5.3.0 and above through 5.10.0; and WSO2 Enterprise Integrator 6.2.0 and above through 6.6.0.
Google and other firms are adding security configuration to software so cloud applications and services have well-defined security settings — a key component of DevSecOps.
Zoho ManageEngine ADSelfService Plus before 6121, ADAuditPlus 7060, Exchange Reporter Plus 5701, and ADManagerPlus 7131 allow NTLM Hash disclosure during certain storage-path configuration steps.
IT departments must account for the business impact and security risks such applications introduce.
Heap buffer overflow issues were found in Opensc before version 0.22.0 in pkcs15-oberthur.c that could potentially crash programs using the library.
Multiple SQL injection vulnerabilities exist in phpGACL 3.3.7. A specially crafted HTTP request can lead to a SQL injection. An attacker can send an HTTP request to trigger this vulnerability.
An exploitable vulnerability exists in the way Pixar OpenUSD 20.05 handles file offsets in binary USD files. A specially crafted malformed file can trigger an arbitrary out-of-bounds memory access that could lead to the disclosure of sensitive information. This vulnerability could be used to bypass mitigations and aid additional exploitation. To trigger this vulnerability, the victim needs to access an attacker-provided file.
An exploitable code execution vulnerability exists in the file format parsing functionality of Graphisoft BIMx Desktop Viewer 2019.2.2328. A specially crafted file can cause a heap buffer overflow resulting in a code execution. An attacker can provide a malicious file to trigger this vulnerability.
A flaw was found in Ansible Galaxy Collections. When collections are built manually, any files in the repository directory that are not explicitly excluded via the ``build_ignore`` list in "galaxy.yml" include files in the ``.tar.gz`` file. This contains sensitive info, such as the user's Ansible Galaxy API key and any secrets in ``ansible`` or ``ansible-playbook`` verbose output without the``no_log`` redaction. Currently, there is no way to deprecate a Collection Or delete a Collection Version. Once published, anyone who downloads or installs the collection can view the secrets.
A flaw was found in WildFly Elytron. A variation to the use of a session fixation exploit when using Undertow was found despite Undertow switching the session ID after authentication.
There is an integer overflow vulnerability in dcraw. When the victim runs dcraw with a maliciously crafted X3F input image, arbitrary code may be executed in the victim's system.
A heap double free issue was found in Opensc before version 0.22.0 in sc_pkcs15_free_tokeninfo.
The ongoing war in Ukraine means that defenses are only as good and as strong as those with whom we partner.